What is SASE?
Introduction to SASE
Network Security has become significantly more important to businesses and service providers in recent years. So, why has security taken on such key importance, and why now?
There has always been a crossover between WAN, Networking and Security but with Applications moving to the Internet and remote working becoming the norm, that crossover has grown in importance.
With the increasing move of applications to the Cloud and of people to working from home, the attack surface for businesses has changed. There is now a need for multiple security solutions at multiple points. More than this, those multiple solutions need to talk to each other: there is a need for an integrated security approach.
We have been watching this happen for a couple of years, and saw it accelerate as people moved to home working during the Covid-19 pandemic.
Networking solutions are edging out to the world of security, as we’ve seen with IPS and Malware Protection. At the same time, companies that specialise in Security are edging into networking.
Businesses need to see network security as a key part of networking and vice versa. At the same time, If networking providers don’t embrace Security then they could see gaps appearing in their offerings, or perhaps their offerings will start to look irrelevant.
What is SASE?
SASE refers to the extension of SD WAN networks to include Security. Think of SASE as the combination of Network as a Service and Network Security as a Service.
Here, for Network as a service, think of SD WAN, and for Network Security as a Service, think of Secure Internet Gateway.
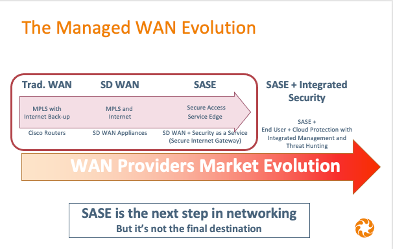
SASE is an evolution in networking services and network security
There has been an ongoing evolution in networking services offered to businesses. We’ve seen traditional networks such as MPLS give way to SD WAN. Now the market is moving towards SASE, to support the need for network security as traffic patterns shift from the HQ and Data centre to cloud, and from branch offices to homes.
SASE will evolve still further, to include additional security functions, managed in an integrated way that allows for automated threat responses and investigations; something that we can think of as “SASE + Integrated security”.
Examples of these additional security functions include email security and endpoint protection.
For example, if a potential phishing attack is identified within an email, an integrated response would cause any email from the same domain to be blocked, and web browser traffic to that domain also to be blocked.
What are the drivers for SASE?
There have been several changes. Let's consider some of the changes to the way that people have been building and locating applications, and to the way that they have been accessing them. We'll consider a typical mid-sized or enterprise business with a WAN based on MPLS.
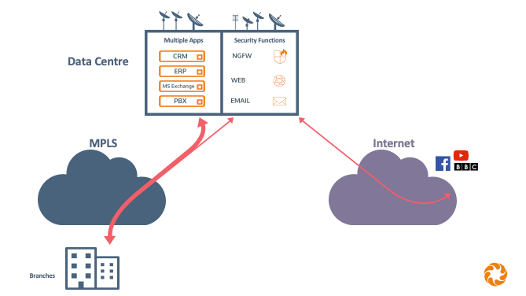
Traditional networks with applications in the Data Centre
In traditional networks, we effectively had primary circuits with backup circuits that weren’t used most of the time. All of the traffic from a branch site went to the HQ or data centre.
From there, perhaps 80% of traffic would have been between the sites and the Data Centre. Maybe 20% of the traffic (general internet browsing and email) would carry on towards the internet, via HQ security functions.
Businesses commonly used internet backup. However, this was typically only used for backup, providing a route back to the HQ or DC to replace a failed MPLS circuit. Thus, it wasn’t typically providing a direct route to internet applications.
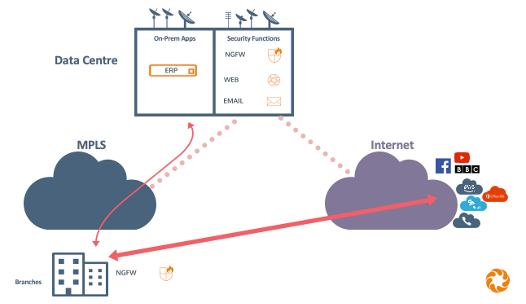
SD WAN improves performance with Direct to Internet traffic
Network providers started to introduce SD WAN, and to use direct internet access as an active circuit, rather than only as a backup. The SD WAN could then route traffic destined for cloud-based applications direct over the internet connection, potentially improving performance.
Of course, with traffic going directly to the internet, an increased level of security was required at the branch level. This has been a key driver in the move towards SASE.
Any traffic that still needed to reach applications in the Data Centre would continue to use the MPLS circuit. With less traffic traversing the MPLS network, these circuits could then potentially be scaled down to smaller bandwidths.
In the event of congestion or circuit failure, SD WAN allowed for traffic to be routed on the best available circuit.
Remote working
Another change has been the increase of working outside the office, whether from home or on the move, something that really took off during the various pandemic lockdowns.
This trend created an increased reliance on the internet, with more traffic that was no longer traversing a Datacentre- or site-based security function. Again, this has been a key driver for SASE.
Since many applications are now outside of the corporate firewall, remote workers who only access cloud applications no longer need to be on the VPN.
Those who do need corporate network access might use a VPN with split tunnelling so that only the DC/HQ traffic needs to be routed that way.
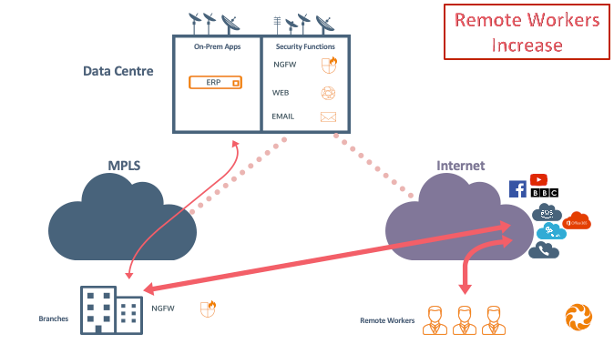
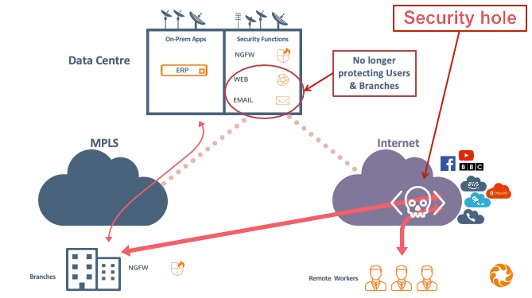
The move to cloud apps and home working has created a security hole
You’ll notice that this has led to a security hole: the branch internet traffic and the remote workers are no longer protected by the advanced security appliances located at the HQ/DC.
And given that our email services are commonly delivered from the cloud, our email security is in the wrong place.
Generally, then, the effect of these changes is that much of our security is in the wrong place.
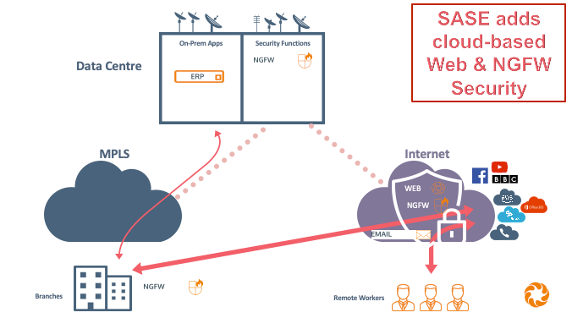
SASE helps to address the security hole
How can people address this security hole?
- We can move Email Security to the cloud.
- But what about Web protection?
- And what about Remote Workers?
What’s needed
- We typically employ Cloud-Based Security to protect Users whether in the Branch or working remotely.
- This is sometimes known as a Secure Internet Gateway.
The emergence of SASE
- SASE was a term that emerged in the industry and was recognised by Gartner to refer to a solution that addresses the security risks posed by these changes.
- So, SASE adds Cloud-based Web security and cloud-based Next-Gen Firewall Security.
SASE is SD WAN, plus Carrier Networks, plus Secure Internet Gateway
Defining SASE
Gartner has recognised the term Secure Access Service Edge, and described how it derives from a market convergence of two broad functions:
- Network as a service (referred to as ‘Connect It’)
- Network Security as a service (referred to as ‘Secure It’)
They see these functions including a number of components:
- Network as a service - which includes components such as SD WAN, Carriers, CDN and WAN Optimisation, as a service.
- Security as a service - which includes components such as Web (DNS) Security, Firewall as a service, Cloud Secure Web Gateway, Zero Trust Network Access.
Is SASE new?
SASE isn't new; the ideas behind it have been around for some time.
For example, one major SD WAN vendor has always positioned the need for network security as a service (such as secure web gateway) alongside their SD WAN offering but has more recently started to refer to this as SASE.
As another example, Cisco has offered SD WAN and Secure Web Gateway within a single licence for a long time.
However, we are seeing the emergence of SASE as a coherent marketing message and expect to see it increasingly also as a coherent commercial offer. We can also see a maturing of SASE from a platform perspective.
What’s next in the SASE journey?
SASE has brought together a range of security products such as NGFW, IPS, AMP, Web Security, Zero Trust Network Access.
These all produce their own alerts, which creates a headache for IT Managers, who can become overwhelmed with information. They need Correlation and the Context of the alerts to help them focus on the important issues.
To illustrate using an example from our home lives.
- You can’t find your car keys;
- You think you left them in your coat pocket;
- But when you look for your coat it’s not there and the front door is open.
These three events may be no cause for alarm when considered in isolation. Taken together, the correlation between them creates a context that means you’ll want to pop outside and make sure your car is still on the drive.
So, with SASE, we have the building blocks, but what we now need is the mortar that binds them together. We see the emergence of Integrated Security, in order to do that.
Once we have that structure, more traditionally separated products, and their alerts can be added to provide further correlation and context. With this, we will then be able to automate responses, leaving IT managers to look at a smaller set of anomalies.
With the emergence of Integrated Security, the ecosystem is becoming more intelligent, using context and correlation to take a more effective and timely response to security threats on the network.